Indirect Command Execution – Penetration Testing Lab
Por um escritor misterioso
Last updated 23 abril 2025

The windows ecosystem provides multiple binaries that could be used by adversaries to execute arbitrary commands that will evade detection especially in environments that are monitoring binaries such as "cmd.exe". In certain occasions the techniques described below could be used to bypass application whitelisting products if rules are not configured properly (whitelist by path or…

Indirect Command Execution: Defense Evasion (T1202) - Hacking Articles
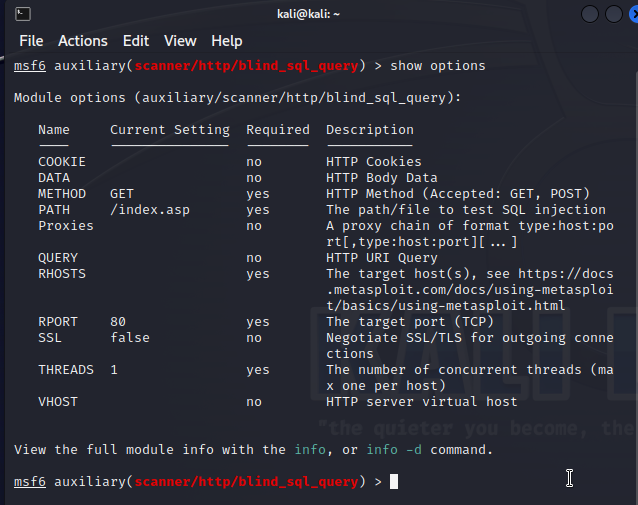
Kali Linux Penetration Testing Tutorial: How to Use Kali Linux

Web Application Penetration Testing: A Practical Guide
PentesterLab: Learn Web App Pentesting!

File Inclusion Vulnerabilities: What are they and how do they work?

Indirect Command Execution – Penetration Testing Lab
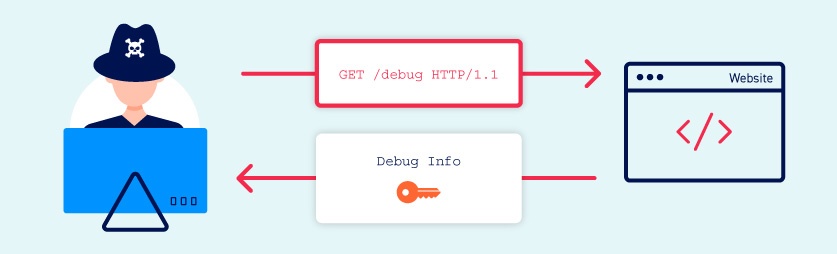
Information disclosure vulnerabilities

GSM/GPRS Traffic Interception for Penetration Testing Engagements, NCC Group Research Blog
Securing LLM Systems Against Prompt Injection

CVE-2021-31956 Exploiting the Windows Kernel (NTFS with WNF) – Part 2, NCC Group Research Blog
Recomendado para você
-
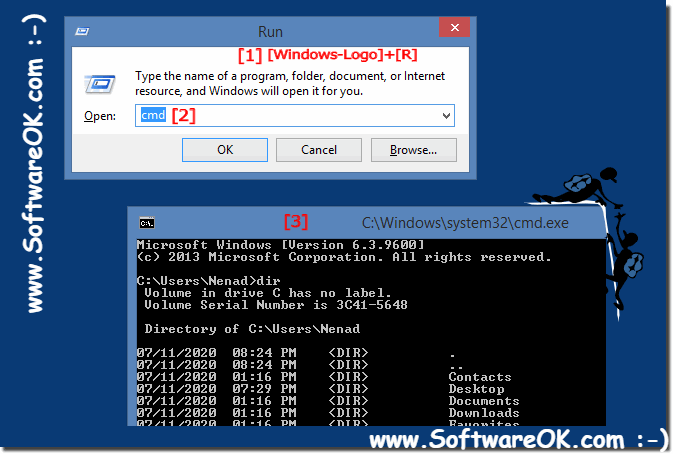 Run cmd.exe the command prompt in administrator mode on Windows 8.1 / 1023 abril 2025
Run cmd.exe the command prompt in administrator mode on Windows 8.1 / 1023 abril 2025 -
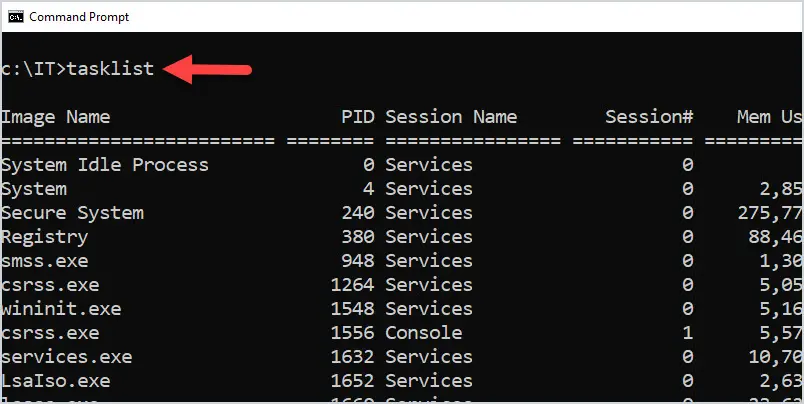
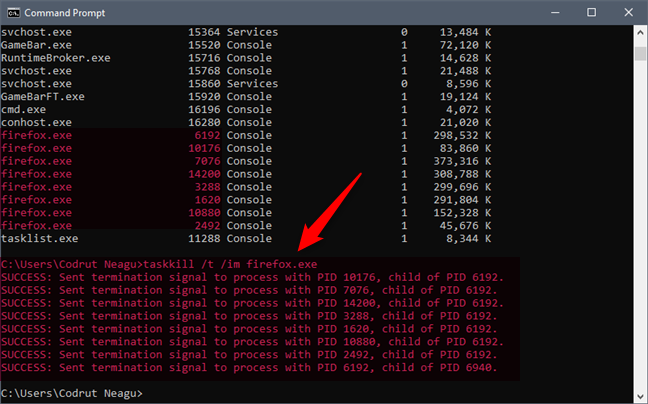 View system information and manage processes from CMD or PowerShell23 abril 2025
View system information and manage processes from CMD or PowerShell23 abril 2025 -
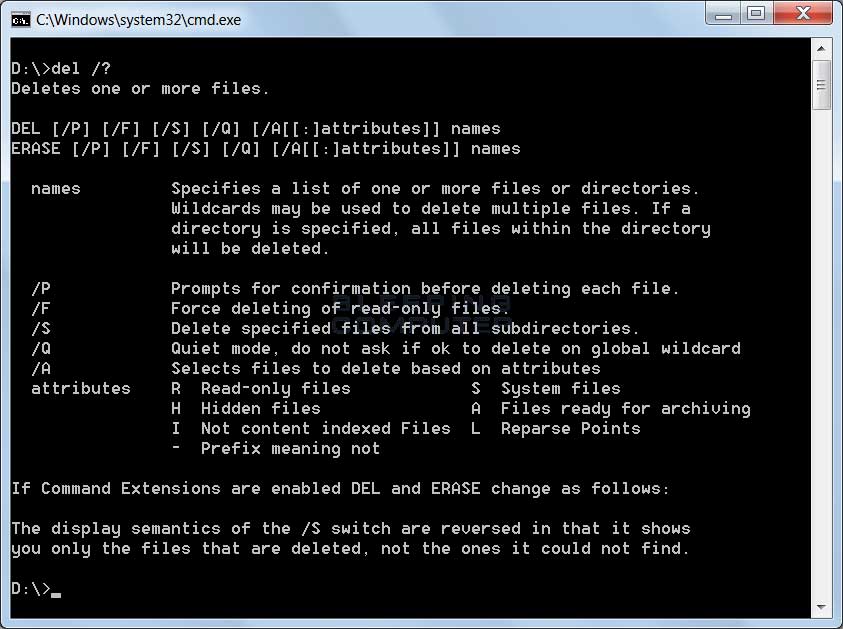 Understanding Command Line Arguments and How to Use Them23 abril 2025
Understanding Command Line Arguments and How to Use Them23 abril 2025 -
 50 Basic Windows Commands with Examples - Active Directory Pro23 abril 2025
50 Basic Windows Commands with Examples - Active Directory Pro23 abril 2025 -
How to run an EXE from command prompt - Quora23 abril 2025
-
 Executing Command Prompt commands in SSIS23 abril 2025
Executing Command Prompt commands in SSIS23 abril 2025 -
How To: Run CMD Commands in a Provisioning Template23 abril 2025
-
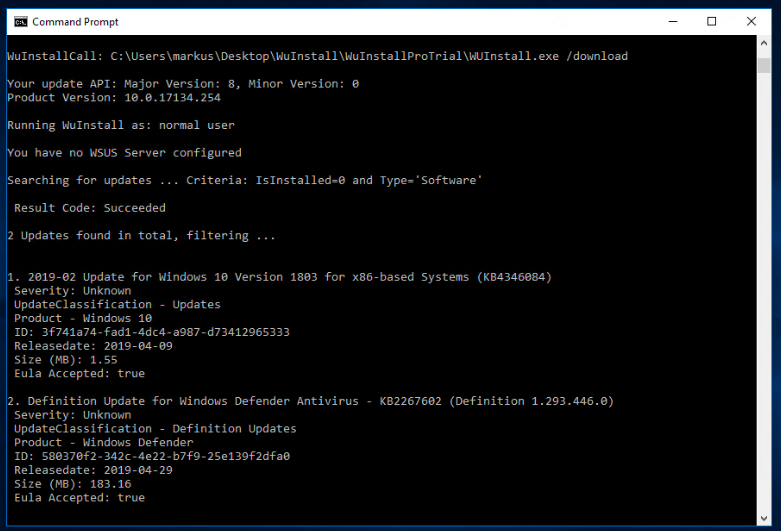 WuInstall - How to force Windows 10 updates to install using the command line23 abril 2025
WuInstall - How to force Windows 10 updates to install using the command line23 abril 2025 -
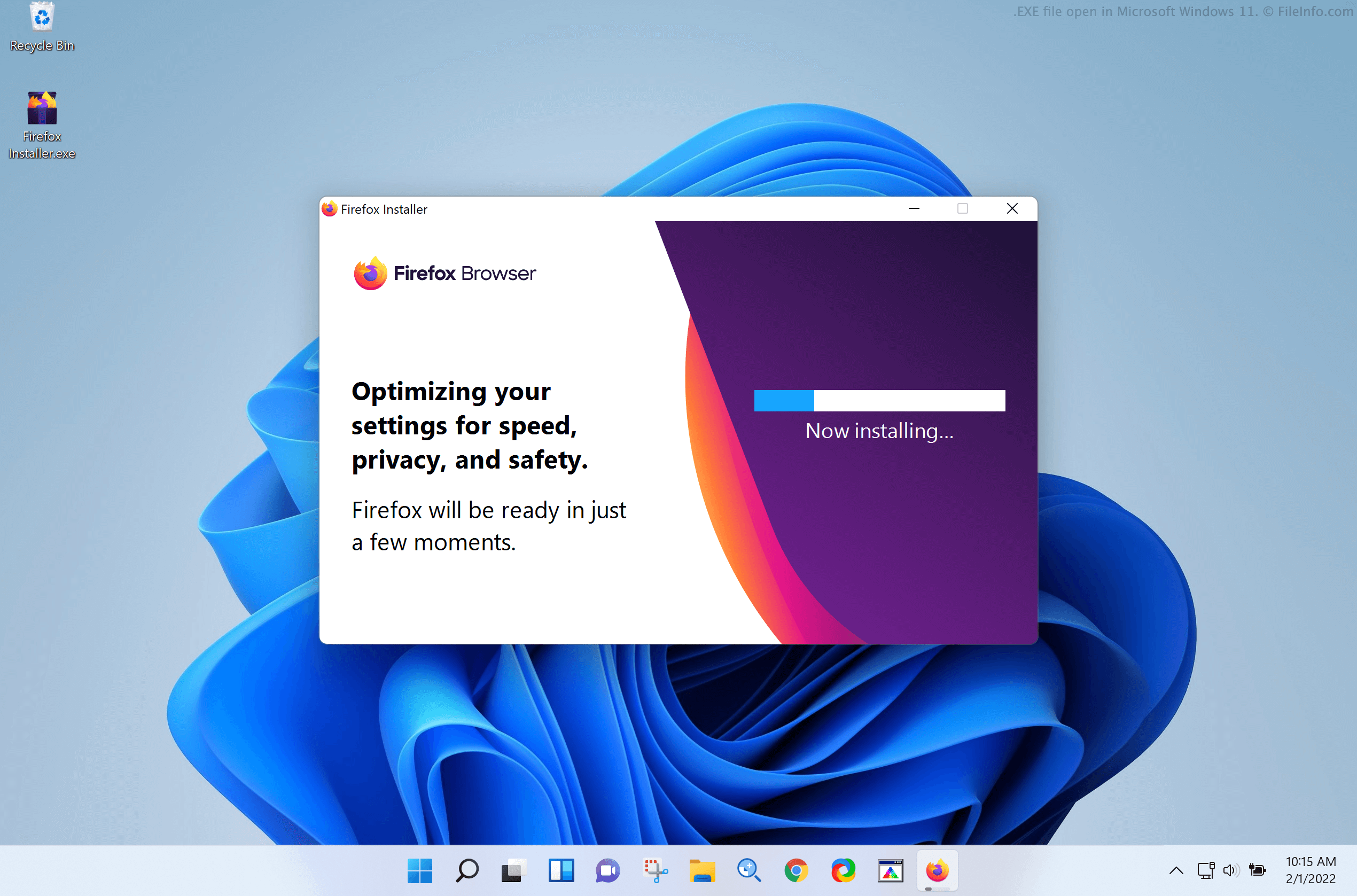 EXE File - What is an .exe file and how do I open it?23 abril 2025
EXE File - What is an .exe file and how do I open it?23 abril 2025 -
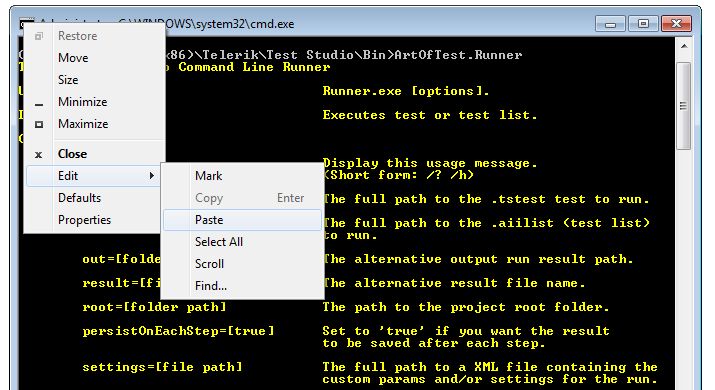 Command Line Runner - Test Studio Dev Documentation - Progress Telerik TestStudio Dev23 abril 2025
Command Line Runner - Test Studio Dev Documentation - Progress Telerik TestStudio Dev23 abril 2025
você pode gostar
-
 Lucky Poke Games from Lucky Poke Games23 abril 2025
Lucky Poke Games from Lucky Poke Games23 abril 2025 -
 Pin by Sala8184 on DragonBall Dragon ball super, Dragon ball super manga, Anime dragon ball super23 abril 2025
Pin by Sala8184 on DragonBall Dragon ball super, Dragon ball super manga, Anime dragon ball super23 abril 2025 -
 Curso de Aberturas de Xadrez: Aprenda a Jogar o Espanhol (também conhe23 abril 2025
Curso de Aberturas de Xadrez: Aprenda a Jogar o Espanhol (também conhe23 abril 2025 -
 Todos os Episódios Fillers do Naruto Shippuden - AnimeNew23 abril 2025
Todos os Episódios Fillers do Naruto Shippuden - AnimeNew23 abril 2025 -
 Preços baixos em The Legend of Zelda: a Link To The Past videogame Guias de Estratégia e cheats23 abril 2025
Preços baixos em The Legend of Zelda: a Link To The Past videogame Guias de Estratégia e cheats23 abril 2025 -
 Super Poser Sonic the Hedgehog Action Figure com 25 pontos articuláveis - Arte em Miniaturas23 abril 2025
Super Poser Sonic the Hedgehog Action Figure com 25 pontos articuláveis - Arte em Miniaturas23 abril 2025 -
/i.s3.glbimg.com/v1/AUTH_08fbf48bc0524877943fe86e43087e7a/internal_photos/bs/2021/q/e/955eHNRkqcUiAibDBrpg/2015-10-02-ninokuni.jpg) Lista reúne os dez melhores jogos de RPG para PlayStation 323 abril 2025
Lista reúne os dez melhores jogos de RPG para PlayStation 323 abril 2025 -
 funny meme sounds by ruki23 abril 2025
funny meme sounds by ruki23 abril 2025 -
 The best Resident Evil 4 Remake weapons23 abril 2025
The best Resident Evil 4 Remake weapons23 abril 2025 -
Yuusha Ga Shinda! - Ver la serie de tv online23 abril 2025