Malware analysis Malicious activity
Por um escritor misterioso
Last updated 13 março 2025

Complex 'NKAbuse' Malware Uses Blockchain to Hide on Linux, IoT

Endpoint Detection and Response, Free - What is EDR Security?

Malware Analysis: Steps & Examples - CrowdStrike

The Guide to Ransomware Solutions in 2023 - Security Boulevard

PROUD-MAL: static analysis-based progressive framework for deep

Endpoint Detection and Response, Free - What is EDR Security?

What Is Malware Analysis? Definition, Types, Stages, and Best

Malware Analysis: Steps & Examples - CrowdStrike

PROUD-MAL: static analysis-based progressive framework for deep
Malware analysis Malicious

Dynamic malware analysis [34]

Interactive Online Malware Sandbox

Malware Analysis: Protecting Your Network from Cyber Attacks

Malware Analysis: Steps & Examples - CrowdStrike
Recomendado para você
-
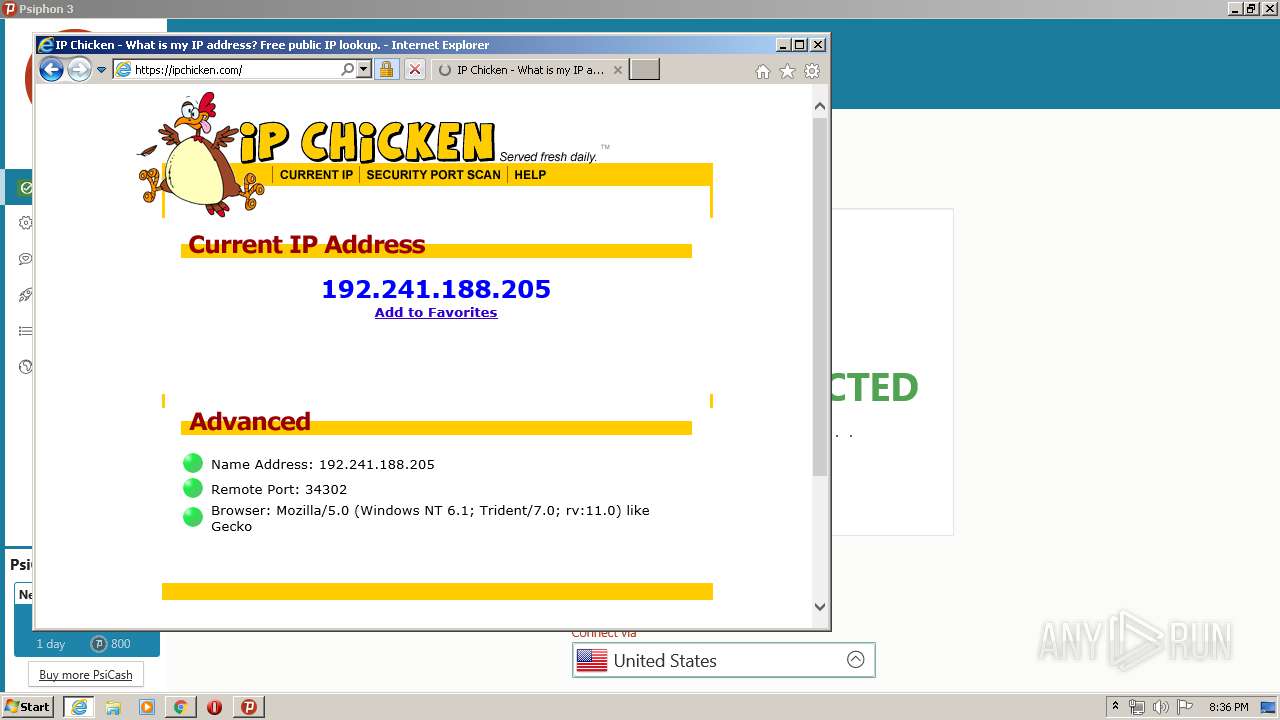
 Show Your Public IP - Restreamer13 março 2025
Show Your Public IP - Restreamer13 março 2025 -
![Question] How to get around VPN blockers?](https://i.gyazo.com/f0c5d0d5b114f0d49954a16dd5112ac7.png) Question] How to get around VPN blockers?13 março 2025
Question] How to get around VPN blockers?13 março 2025 -
 Cyber portfolio13 março 2025
Cyber portfolio13 março 2025 -
![Zscaler- Source IP Anchoring [SIPA]](https://i.ytimg.com/vi/ylt74TZnS2Q/hq720.jpg?sqp=-oaymwE7CK4FEIIDSFryq4qpAy0IARUAAAAAGAElAADIQj0AgKJD8AEB-AH-CIAC0AWKAgwIABABGDwgEyh_MA8=&rs=AOn4CLAOEq5hhRYj-Kw0ehVImE5Q4ZxLDQ) Zscaler- Source IP Anchoring [SIPA]13 março 2025
Zscaler- Source IP Anchoring [SIPA]13 março 2025 -
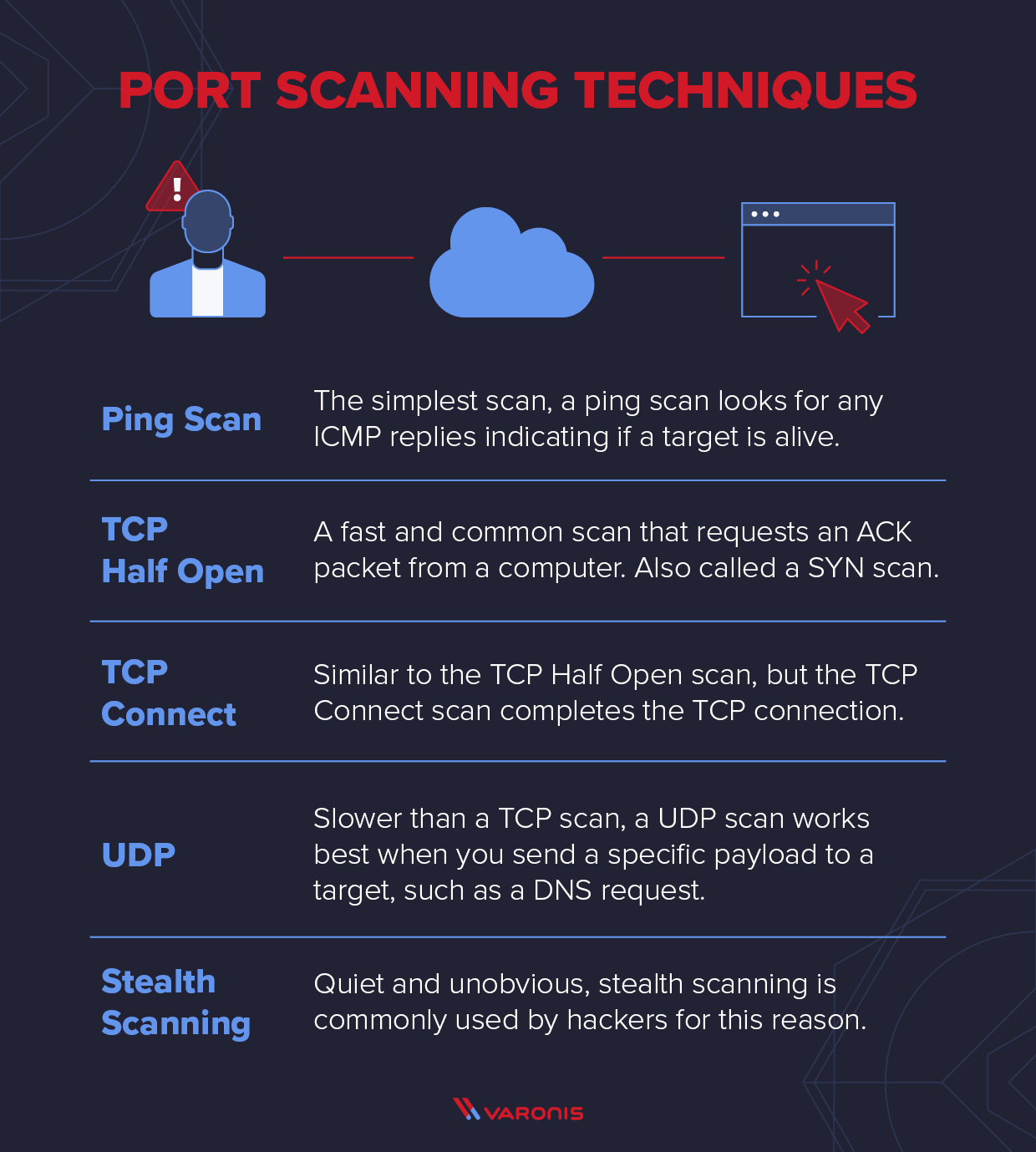 Explaining Port Scanning. A port scan is a common technique…, by Arth Awasthi13 março 2025
Explaining Port Scanning. A port scan is a common technique…, by Arth Awasthi13 março 2025 -
 What is port scanning and how does it work?13 março 2025
What is port scanning and how does it work?13 março 2025 -
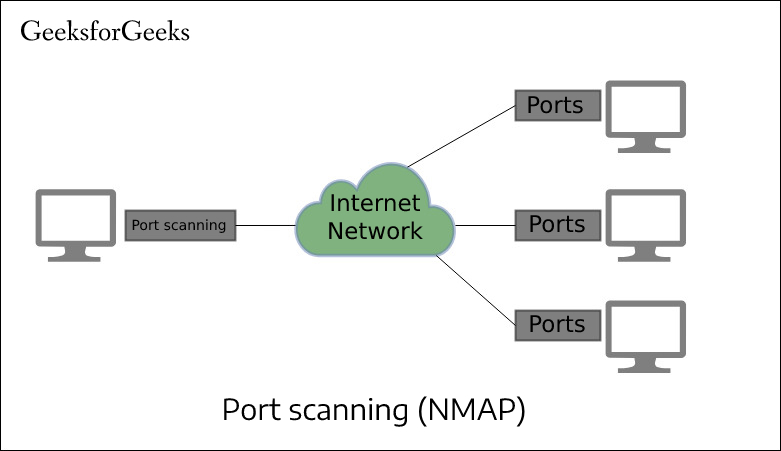 Port Scan in Ethical Hacking - GeeksforGeeks13 março 2025
Port Scan in Ethical Hacking - GeeksforGeeks13 março 2025 -
 What is Tor Browser & How to Setup Tor13 março 2025
What is Tor Browser & How to Setup Tor13 março 2025 -
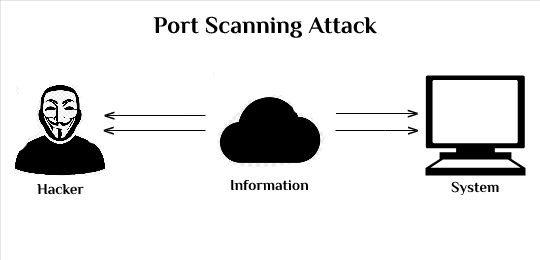 How to Prevent Port Scan Attacks? - GeeksforGeeks13 março 2025
How to Prevent Port Scan Attacks? - GeeksforGeeks13 março 2025 -
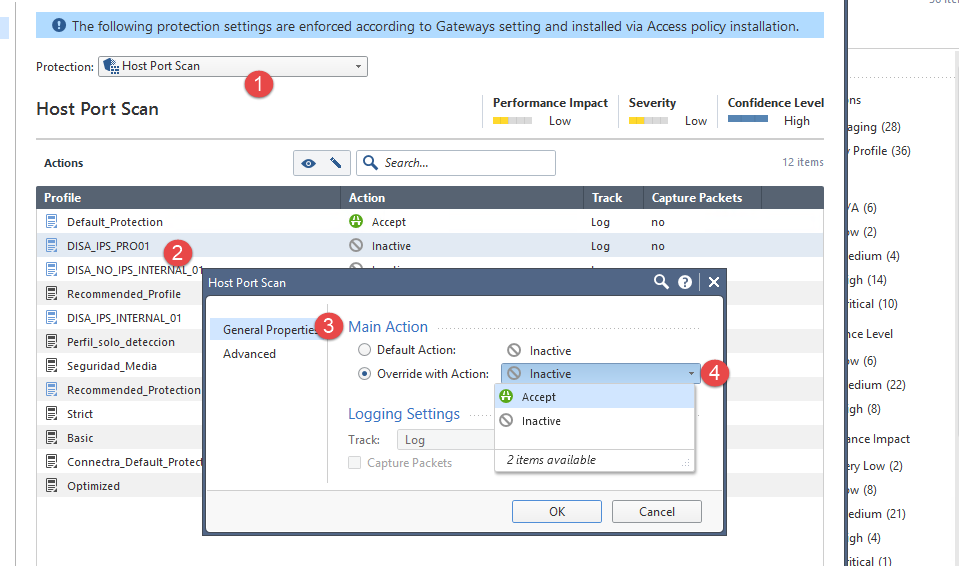 How can I avoid Host Port scan? - Check Point CheckMates13 março 2025
How can I avoid Host Port scan? - Check Point CheckMates13 março 2025
você pode gostar
-
Brinquedos caminhão carretinha com trator em madeira mdf infantil13 março 2025
-
 Kamado Tanjiro, Kimetsu no Yaiba13 março 2025
Kamado Tanjiro, Kimetsu no Yaiba13 março 2025 -
 Baconese Maionese De Bacon + Maionese Grill 350g Junior13 março 2025
Baconese Maionese De Bacon + Maionese Grill 350g Junior13 março 2025 -
free limited hair 2023|TikTok Search13 março 2025
-
 Quando é o próximo jogo da seleção brasileira feminina?13 março 2025
Quando é o próximo jogo da seleção brasileira feminina?13 março 2025 -
 The Ending Of Ragnarok Season 2 Explained13 março 2025
The Ending Of Ragnarok Season 2 Explained13 março 2025 -
 Boykisser (meme) + Roblox smug face xbox emblem (ID: BE2NT98WX8NZ13 março 2025
Boykisser (meme) + Roblox smug face xbox emblem (ID: BE2NT98WX8NZ13 março 2025 -
 Shiny Hitmonlee i got today. hoping for a makuhita shiny : r/pokemongo13 março 2025
Shiny Hitmonlee i got today. hoping for a makuhita shiny : r/pokemongo13 março 2025 -
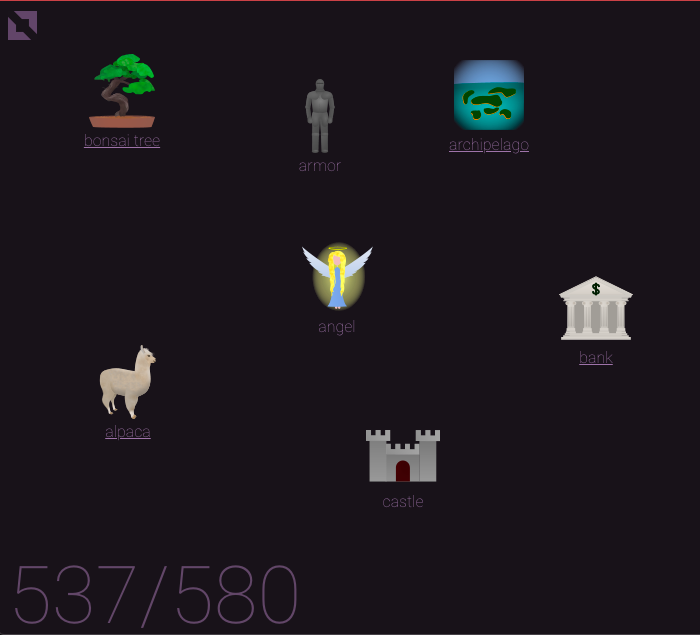 Little Alchemy – the Square13 março 2025
Little Alchemy – the Square13 março 2025 -
 Link Nonton Anime Saikyou Onmyouji no Isekai Tenseiki Episode 1213 março 2025
Link Nonton Anime Saikyou Onmyouji no Isekai Tenseiki Episode 1213 março 2025

