Malware analysis Malicious activity
Por um escritor misterioso
Last updated 10 março 2025

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

Playbook for Malware outbreak

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

AV-TEST Confirms Skyhigh Security Service Edge Delivers Superior Threat Protection in All Test Categories
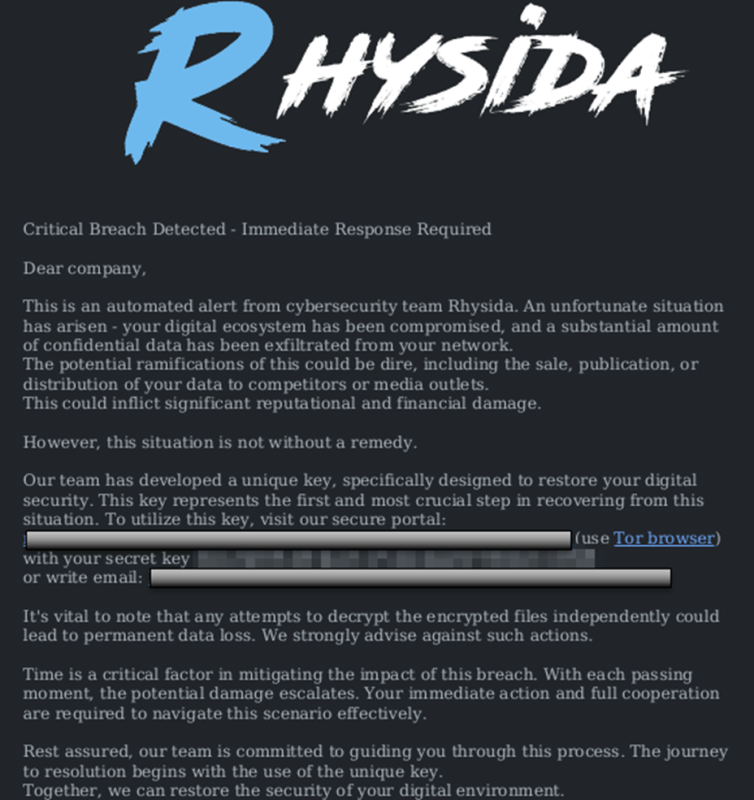
StopRansomware: Rhysida Ransomware

Detail procedure of malware analysis

MetaDefender Cloud Advanced threat prevention and detection

PROUD-MAL: static analysis-based progressive framework for deep unsupervised malware classification of windows portable executable

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

U.S. law enforcement seizes BlackCat ransomware site, distributes decryption key

Interactive Online Malware Sandbox

What to Include in a Malware Analysis Report
Recomendado para você
-
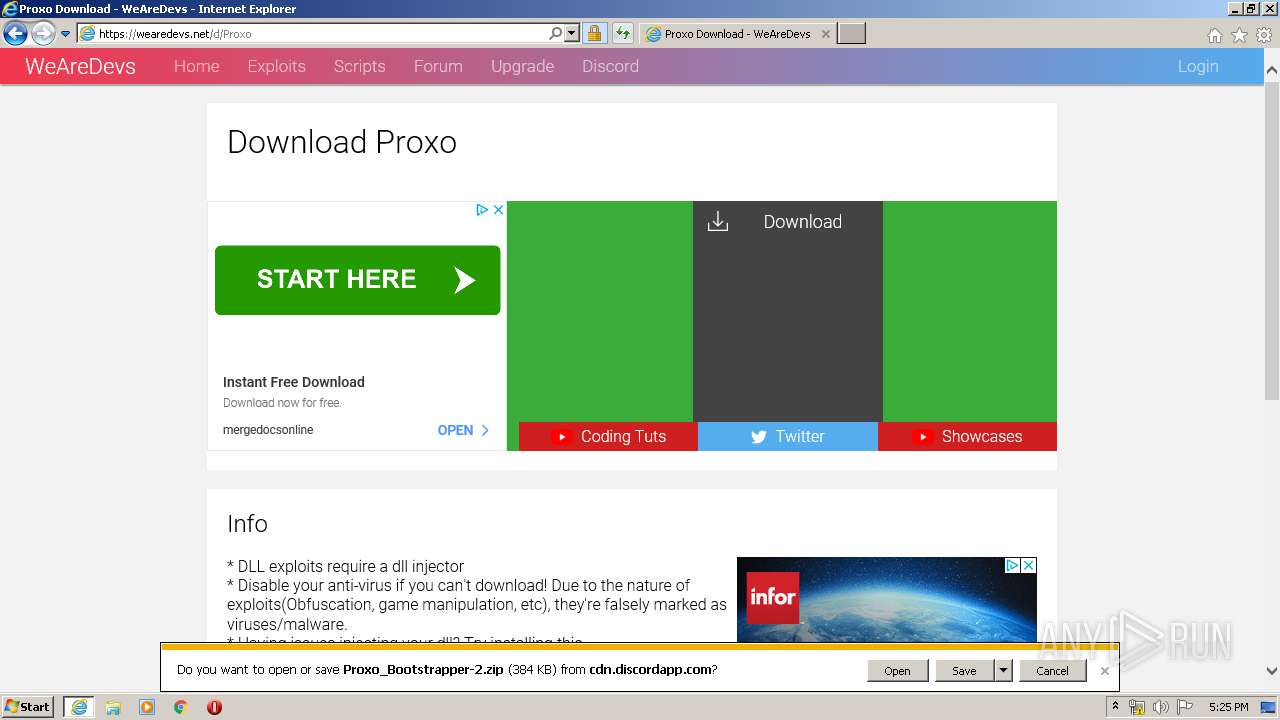
 WeAreDevs (@WeAreDevs_) / X10 março 2025
WeAreDevs (@WeAreDevs_) / X10 março 2025 -
 Wearedevs10 março 2025
Wearedevs10 março 2025 -
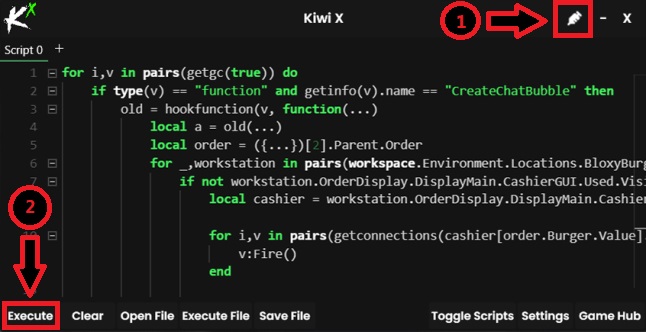 Kiwi X Free Download For Windows PC - Softlay10 março 2025
Kiwi X Free Download For Windows PC - Softlay10 março 2025 -
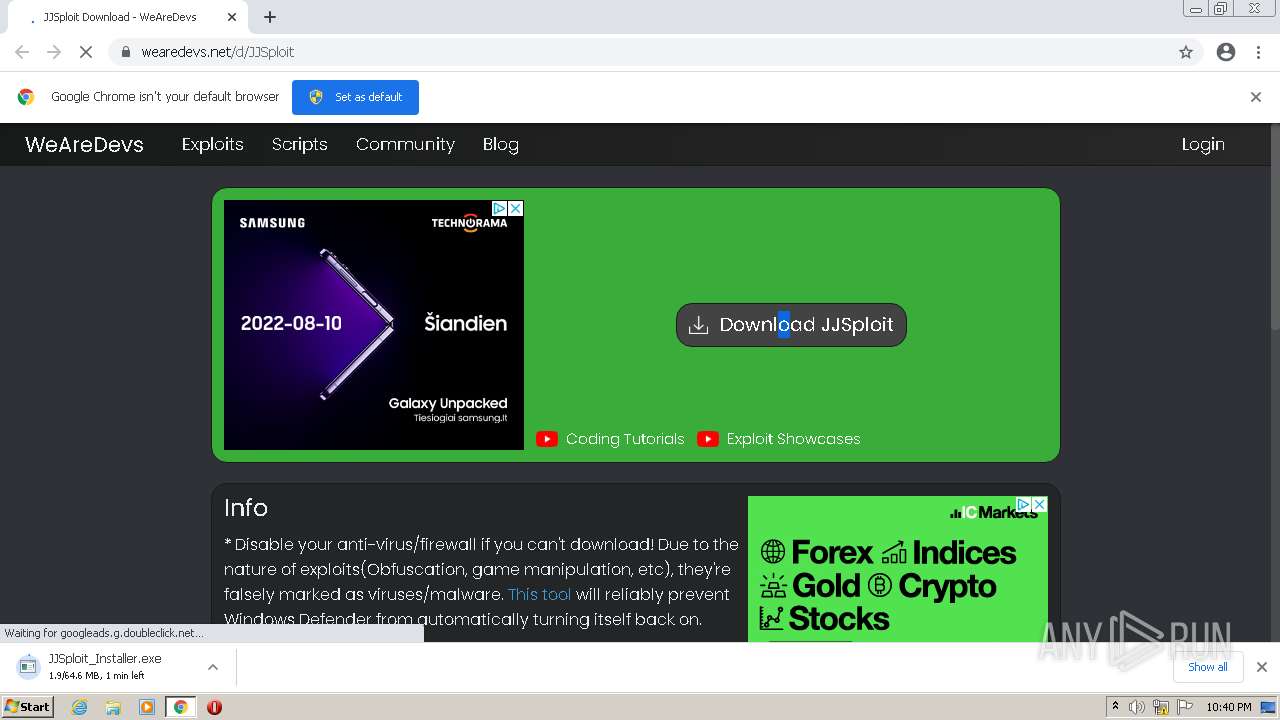
 How to use lua scripts with JJ sploit (By wearedevs)10 março 2025
How to use lua scripts with JJ sploit (By wearedevs)10 março 2025 -
roblox-executor · GitHub Topics · GitHub10 março 2025
-
 Malware analysis Malicious activity10 março 2025
Malware analysis Malicious activity10 março 2025 -
 IT Pro Tuesday #19010 março 2025
IT Pro Tuesday #19010 março 2025 -
roblox #fyo #hack #script #jjsploit #wearedevs Like and Comment10 março 2025
-
 Exploiter kicking everyone from the server, how to find who10 março 2025
Exploiter kicking everyone from the server, how to find who10 março 2025 -
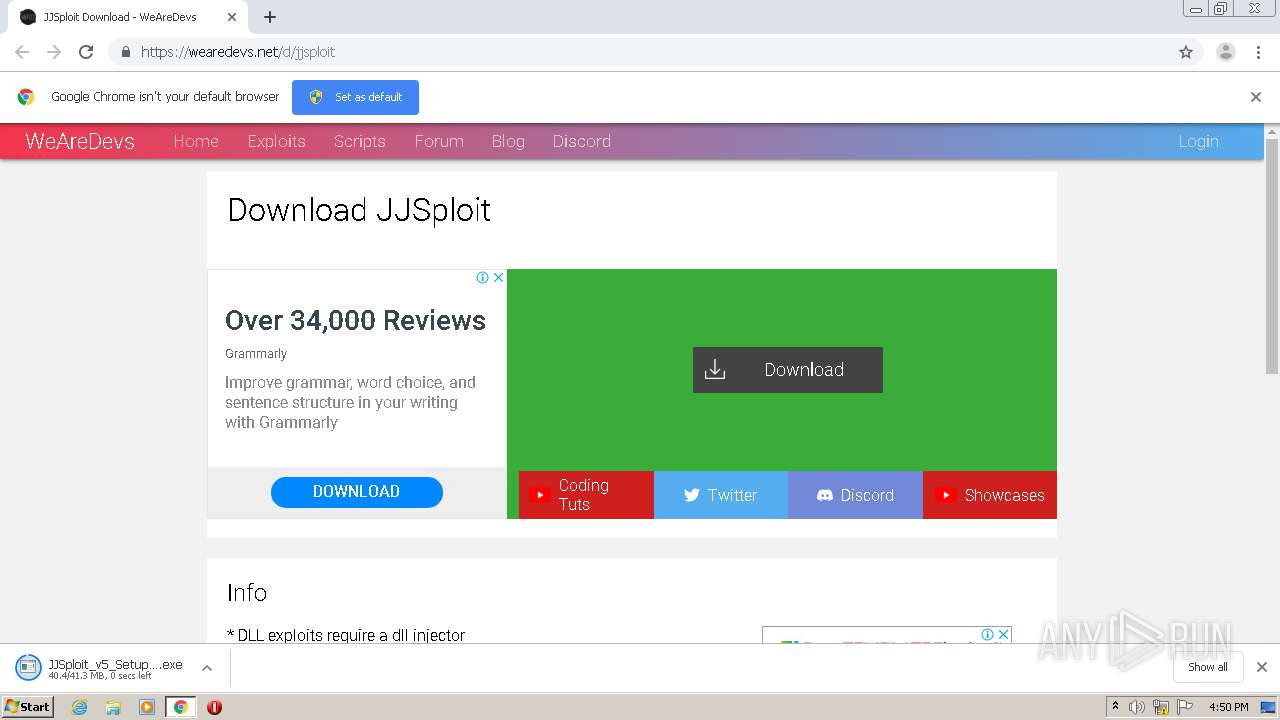 Malware analysis Malicious10 março 2025
Malware analysis Malicious10 março 2025
você pode gostar
-
 The new Sonic game looks too bad to be true10 março 2025
The new Sonic game looks too bad to be true10 março 2025 -
 Iruka Umino Umino Iruka GIF - Iruka umino Umino iruka Iruka - Discover & Share GIFs10 março 2025
Iruka Umino Umino Iruka GIF - Iruka umino Umino iruka Iruka - Discover & Share GIFs10 março 2025 -
 Steam Deck Review Best Handheld Gaming PC 202310 março 2025
Steam Deck Review Best Handheld Gaming PC 202310 março 2025 -
 Fire Force (TV Series 2019– ) - IMDb10 março 2025
Fire Force (TV Series 2019– ) - IMDb10 março 2025 -
 Elfen Lied Poster Anime Lucy Girl New Human Blood Ken Art Manga Print 16x20 Inches10 março 2025
Elfen Lied Poster Anime Lucy Girl New Human Blood Ken Art Manga Print 16x20 Inches10 março 2025 -
 Minecraft Live 2021 Mobs Vote: Copper Golem, Allay, And The Glare10 março 2025
Minecraft Live 2021 Mobs Vote: Copper Golem, Allay, And The Glare10 março 2025 -
 Folding Magnetic International Chess Magnetic International Chess10 março 2025
Folding Magnetic International Chess Magnetic International Chess10 março 2025 -
 Alphabet lore in Ohio part 6 W-X - Comic Studio10 março 2025
Alphabet lore in Ohio part 6 W-X - Comic Studio10 março 2025 -
 Seller Stories: Meet Jon-Luc10 março 2025
Seller Stories: Meet Jon-Luc10 março 2025 -
 Total Drama: All Stars - Desciclopédia10 março 2025
Total Drama: All Stars - Desciclopédia10 março 2025
